
Phishing Attacks: Best Practices to Identify & Mitigate Cyber Threats
Phishing attacks are one of the most prevalent cybersecurity threats today. They exploit human psychology to trick individuals into revealing sensitive information such as passwords, credit card numbers, or other personal data. Understanding how to identify and mitigate these attacks is crucial for both individuals and organizations.
Identifying Phishing Attacks
Phishing attacks can be sophisticated, leveraging advanced techniques to deceive even the most cautious individuals. However, there are several common signs that can help in identifying potential phishing attempts. Understanding these indicators is crucial in protecting yourself and your organization from falling victim to these schemes. Here are some detailed characteristics to watch out for:
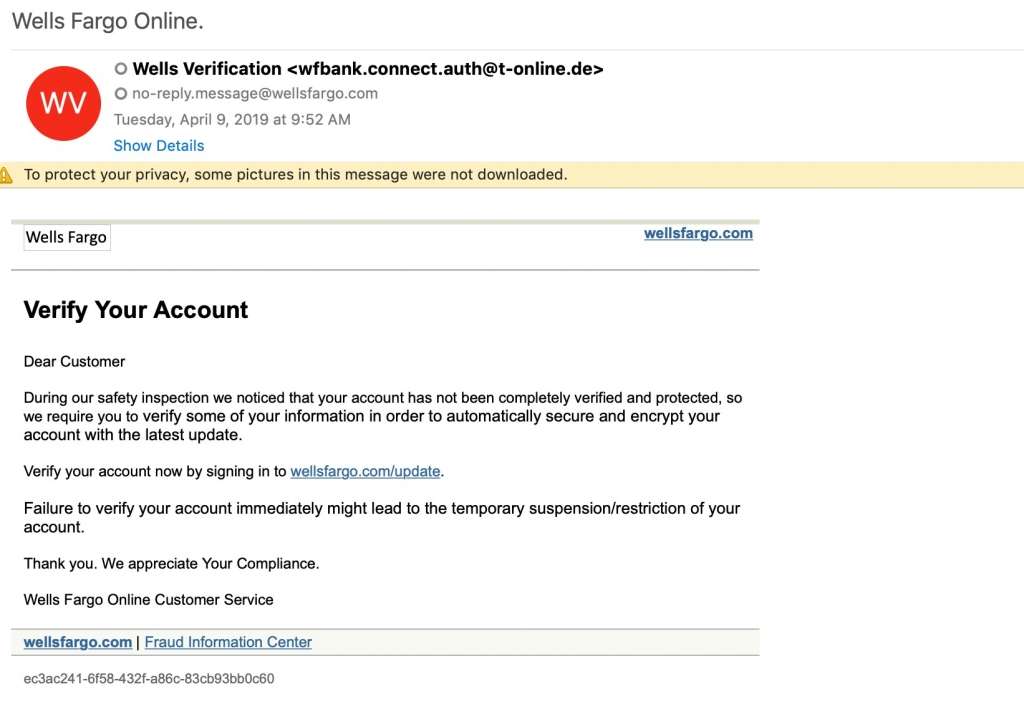
- Suspicious Sender:
- Emails from unknown senders or those with strange, misspelled, or spoofed email addresses should raise a red flag. For example, an email purportedly from your bank but with an email address like “[email protected]” is suspicious.
- Additionally, be wary of emails from legitimate sources but sent at unusual times or with abnormal content.
- Urgent Language:
- Phishing emails often use urgent or alarming language to create a sense of panic and prompt immediate action. Phrases like “Your account will be suspended unless you act now!” or “Immediate action required to secure your account!” are common.
- This tactic exploits the recipient’s fear of negative consequences to bypass rational scrutiny and get them to click on malicious links or provide sensitive information quickly.
- Generic Greetings:
- Be cautious of emails that use generic greetings such as “Dear Customer” or “Dear User” instead of addressing you by your name. Legitimate organizations usually personalize their communications.
- This lack of personalization can be a sign that the email is being sent to a large number of recipients as part of a phishing campaign.
- Unusual Links:
- Before clicking on any link, hover your mouse over it to reveal the actual URL. If the displayed URL is different from what is shown in the email or if it looks suspicious, do not click on it.
- Phishing links often lead to websites designed to look like legitimate ones but have subtle differences, such as misspelled domains (e.g., “www.paypa1.com” instead of “www.paypal.com“).
- Unexpected Attachments:
- Be wary of unsolicited attachments, especially if they come from unknown senders or if the email itself looks suspicious. Attachments can contain malware, ransomware, or other malicious software that can compromise your computer and personal information.
- Common attachment file types used in phishing attacks include .exe, .zip, .doc, and .pdf files. Always verify with the sender through another communication channel before opening any unexpected attachments.
By paying close attention to these details, you can significantly reduce the risk of falling victim to phishing attacks. Always take a moment to scrutinize emails, even if they appear to be from familiar sources, and err on the side of caution when it comes to sharing personal or sensitive information online.
Types of Phishing Attacks
Understanding the various forms of phishing is crucial for recognizing and defending against these malicious tactics. Each type of phishing attack has unique characteristics and targets, making it essential to be aware of their differences. Here are the main types of phishing attacks explained in detail:
- Email Phishing:
- This is the most common form of phishing, where attackers send fraudulent emails that appear to come from reputable sources.
- These emails often contain malicious links or attachments designed to steal personal information or install malware on the recipient’s device.
- Common scenarios include fake notifications from banks, online stores, or popular services like PayPal, urging the recipient to verify their account or reset their password.
- The email may contain official-looking logos and branding to appear legitimate, making it more convincing.
- Spear Phishing:
- Unlike generic phishing attacks, spear phishing is highly targeted and aimed at specific individuals or organizations.
- Attackers conduct extensive research to gather personal information about the target, such as their name, position, and contacts, to create a tailored message.
- These emails often appear to come from a trusted source, such as a colleague, boss, or business partner, increasing the likelihood of the target falling for the scam.
- For example, an employee might receive an email that seems to come from their manager, requesting sensitive information or instructing them to click on a malicious link.
- Whaling:
- Whaling targets high-profile individuals within an organization, such as executives, CEOs, or other senior officials, with personalized and sophisticated messages.
- These attacks often involve more effort and research, as the rewards can be significantly higher due to the access and authority these individuals possess.
- Whaling emails typically focus on urgent or high-stakes issues, such as legal matters, corporate policies, or executive decisions, making them more convincing.
- An example of whaling could be a fraudulent email appearing to be from the company’s legal team, asking the executive to review a confidential document related to a legal case.
- Smishing and Vishing:
- Smishing (SMS phishing) and vishing (voice phishing) are variations of phishing that use SMS and voice calls, respectively, to steal information.
- Smishing:
- Attackers send text messages that appear to be from reputable sources, containing malicious links or requests for personal information.
- Common tactics include fake delivery notifications, alerts about account issues, or offers for prizes and rewards.
- For example, a text message might claim to be from a bank, asking the recipient to verify their account by clicking on a link and entering their login details.
- Vishing:
- Attackers use voice calls to impersonate legitimate entities, such as banks, government agencies, or tech support.
- They often create a sense of urgency or fear to trick the recipient into providing sensitive information, such as credit card numbers or Social Security numbers.
- An example of vishing could be a caller pretending to be from the IRS, threatening legal action unless the recipient provides their personal information over the phone.

By understanding these different types of phishing attacks, individuals and organizations can better recognize the signs and take appropriate measures to protect themselves. It is important to remain vigilant and cautious when receiving unsolicited communications, whether through email, SMS, or phone calls, and to verify the legitimacy of any requests for personal information.
Mitigating Phishing Attacks
Mitigation strategies are essential to protect against phishing attacks. A comprehensive approach involves a combination of education, technical measures, and robust policies and procedures. Here are detailed strategies to effectively mitigate phishing risks:
- Education and Awareness:
- Regular Training for Employees:
- Conduct regular training sessions to educate employees about the latest phishing techniques and how to recognize them.
- Training should cover identifying suspicious emails, the importance of scrutinizing links and attachments, and the dangers of providing personal information without verification.
- Employees should be encouraged to report any suspicious emails or activities immediately.
- Simulated Phishing Exercises:
- Implement simulated phishing exercises to test employees’ ability to recognize and respond to phishing attempts.
- These exercises can help identify weaknesses in awareness and provide opportunities for further training.
- By mimicking real phishing attacks, employees can practice their responses in a controlled environment, improving their readiness for actual threats.
- Regular Training for Employees:
- Technical Measures:
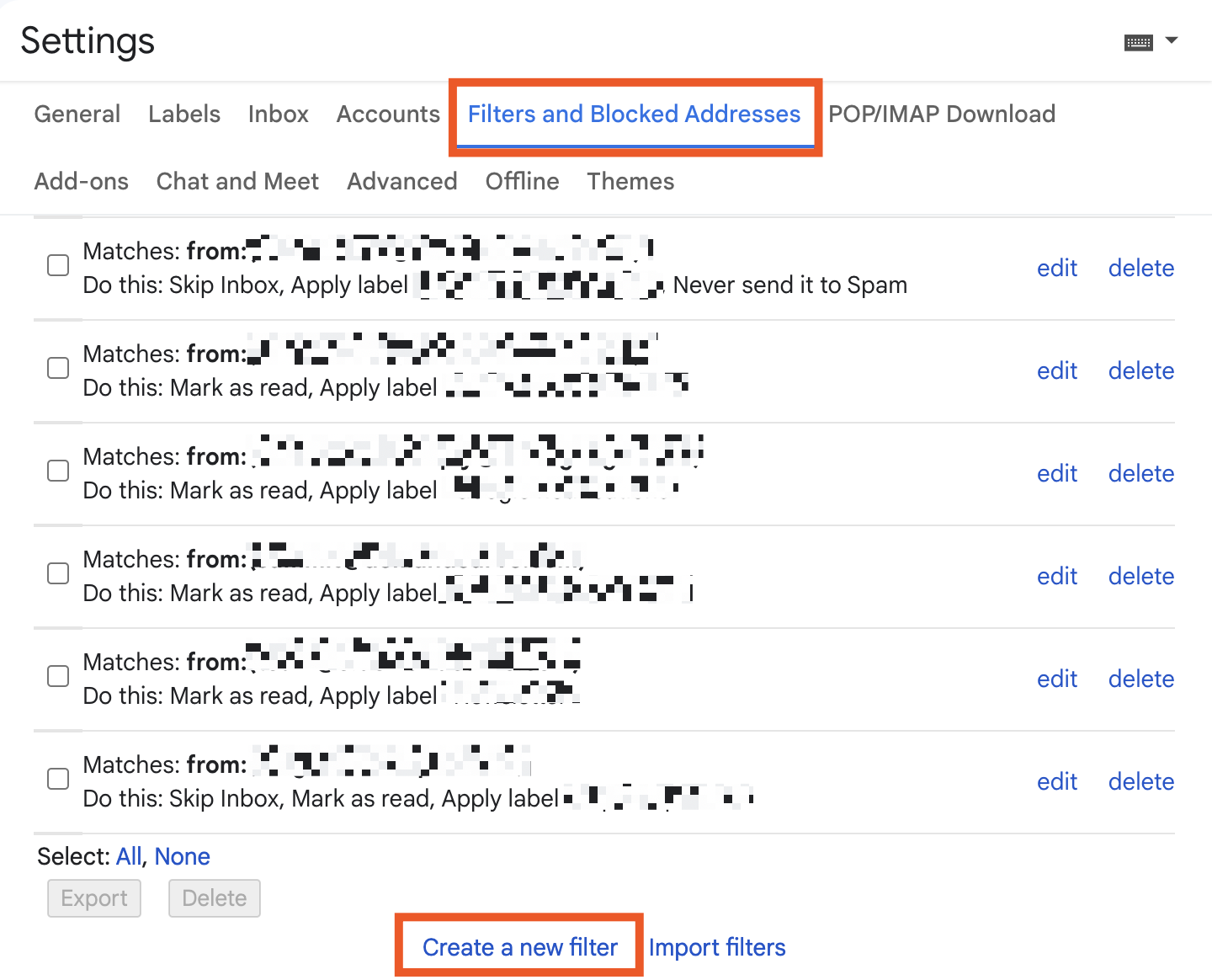
- Implementing Email Filters:
- Use advanced email filtering solutions to block or quarantine suspicious emails before they reach employees’ inboxes.
- These filters can detect and block emails based on known phishing patterns, blacklisted IP addresses, and suspicious content.
- Regularly update the filtering rules to adapt to new phishing tactics.
- Implementing Email Filters:
- Using Multi-Factor Authentication (MFA):
- Implement MFA for all sensitive accounts to add an extra layer of security.
- Even if an attacker obtains a password, they will be unable to access the account without the second authentication factor, such as a code sent to a mobile device.
- MFA significantly reduces the risk of unauthorized access due to compromised credentials.
- Keeping Software and Systems Updated:
- Regularly update all software and systems to patch vulnerabilities that could be exploited by phishing attacks.
- Ensure that all devices, including computers, smartphones, and network equipment, have the latest security patches and updates installed.
- Use automated update management tools to streamline the process and reduce the likelihood of human error.
- Policy and Procedures:
- Establishing Clear Protocols for Reporting Phishing Attempts:
- Develop and communicate clear procedures for reporting suspected phishing emails or incidents.
- Employees should know who to contact and what steps to take if they receive a suspicious email or notice unusual activity.
- Encourage a culture of transparency and prompt reporting to minimize the impact of phishing attacks.
- Ensuring Employees Verify Requests for Sensitive Information:
- Establish policies requiring employees to verify the authenticity of any request for sensitive information through secondary channels.
- For example, if an email requests sensitive information, employees should call the requester using a known, trusted phone number to confirm the request.
- This additional step helps prevent falling victim to phishing attacks that rely on impersonation and social engineering.
- Establishing Clear Protocols for Reporting Phishing Attempts:
By combining these strategies, organizations can create a robust defense against phishing attacks. Education and awareness empower employees to recognize and respond to threats, while technical measures and strong policies provide multiple layers of protection. Regularly reviewing and updating these strategies ensures they remain effective against evolving phishing tactics, safeguarding both individuals and organizations from potential harm.
Responding to a Phishing Attack
In case of a suspected phishing attack, swift and decisive action is critical to minimize potential damage. Here are detailed steps to take immediately if you believe you have encountered a phishing attempt:
- Do Not Engage:
- Avoid Clicking on Links or Downloading Attachments:
- Do not click on any links, buttons, or attachments in the suspicious email. Even a single click can lead to malware installation or redirect you to a fraudulent website designed to steal your information.
- Be cautious with any action the email prompts you to take, such as filling out forms or providing personal information.
- If you have already clicked on a link, avoid entering any information on the resulting webpage and close the browser immediately.
- Avoid Clicking on Links or Downloading Attachments:
- Report Immediately:
- Notify Your IT Department or Security Team:
- Contact your organization’s IT department or security team as soon as possible. Provide them with details about the suspicious email, including the sender’s address, subject line, and any actions you have taken.
- Forward the suspicious email to the designated security email address within your organization so that they can analyze it and take appropriate measures.
- Reporting the incident helps the IT team alert other employees and implement measures to prevent further exposure.
- Notify Your IT Department or Security Team:
- Change Credentials:
- If You Suspect Your Information Has Been Compromised, Change Passwords Immediately:
- If you believe you have inadvertently provided your credentials or other sensitive information, change your passwords immediately for the affected accounts.
- Use strong, unique passwords for each account, incorporating a mix of letters, numbers, and special characters.
- Consider using a password manager to generate and store secure passwords.
- Enable multi-factor authentication (MFA) on your accounts to add an extra layer of security.

- If You Suspect Your Information Has Been Compromised, Change Passwords Immediately:
- Monitor Accounts:
- Keep an Eye on Your Accounts for Any Suspicious Activity:
- Regularly monitor your bank accounts, credit card statements, and online accounts for any unauthorized transactions or changes.
- Set up alerts on your accounts to receive notifications of any unusual activity, such as login attempts from unfamiliar locations or large transactions.
- If you notice any suspicious activity, report it to the relevant institution immediately. For financial accounts, contact your bank or credit card company to discuss the potential need for account freezes or further protective measures.
- Keep an Eye on Your Accounts for Any Suspicious Activity:
By following these steps, you can significantly reduce the risk and impact of a phishing attack. Quick and effective action not only protects your personal information but also helps safeguard your organization from broader security breaches. It’s essential to remain vigilant and proactive in responding to any suspicious activities, ensuring that both you and your organization are well-prepared to handle phishing threats.
Tools and Resources
Several tools and resources can assist in defending against phishing attacks, providing multiple layers of protection to safeguard individuals and organizations from these threats. Leveraging the right combination of technology and educational resources can significantly enhance your defense strategy. Here are some essential tools and resources explained in detail:
- Email Security Solutions:
- Products like Proofpoint and Mimecast Offer Advanced Email Protection:
- Proofpoint:
- Provides comprehensive email security by filtering out spam, phishing emails, and other malicious content before it reaches your inbox.
- Features advanced threat detection capabilities that use machine learning and threat intelligence to identify and block sophisticated phishing attempts.
- Offers data loss prevention (DLP) features to protect sensitive information and ensure compliance with regulations.
- Includes user-friendly reporting tools and dashboards to monitor and manage email security incidents.
- Mimecast:
- Delivers robust email security through a cloud-based platform that blocks phishing, malware, and impersonation attacks.
- Employs advanced heuristics and threat intelligence to detect and prevent email-borne threats in real-time.
- Provides archiving and continuity services, ensuring access to email even during outages or attacks.
- Integrates with existing security infrastructure to enhance overall threat detection and response capabilities.

- Proofpoint:
- Products like Proofpoint and Mimecast Offer Advanced Email Protection:
- Browser Extensions:
- Tools like Netcraft and Web of Trust Help Identify Malicious Websites:
- Netcraft:
- Offers a browser extension that provides real-time protection against phishing attacks by blocking access to known malicious websites.
- Continuously updates its database with new threats, ensuring users are protected from the latest phishing sites.
- Displays a site’s risk rating and provides detailed information about the site’s history and ownership, helping users make informed decisions.
- Users can report suspicious sites directly through the extension, contributing to the collective defense against phishing.
- Web of Trust (WOT):
- A community-driven browser extension that rates websites based on their trustworthiness, vendor reliability, privacy, and child safety.
- Users can see color-coded icons next to links, indicating the site’s reputation and potential risk.
- Provides detailed reviews and ratings from other users, helping individuals avoid potentially dangerous websites.
- Offers protection against phishing, scams, malware, and other online threats by alerting users before they visit risky sites.
- Netcraft:
- Tools like Netcraft and Web of Trust Help Identify Malicious Websites:
- Awareness Programs:
- Organizations like the Anti-Phishing Working Group (APWG) Provide Valuable Resources and Training Materials:
- Anti-Phishing Working Group (APWG):
- A global coalition focused on unifying the global response to cybercrime, particularly phishing attacks.
- Provides extensive resources, including research papers, trend reports, and best practice guides on phishing and cybersecurity.
- Offers training materials and awareness programs designed to educate individuals and organizations about the latest phishing tactics and how to defend against them.
- Organizes conferences and workshops that bring together industry experts, researchers, and policymakers to collaborate on anti-phishing strategies and solutions.
- StaySafeOnline by the National Cyber Security Alliance (NCSA):
- Provides resources for individuals and businesses to improve their cybersecurity practices, including guidelines for recognizing and avoiding phishing attacks.
- Offers educational materials, such as infographics, webinars, and toolkits, to raise awareness about online safety and security.
- Promotes campaigns like Cybersecurity Awareness Month to engage and educate the public on the importance of cybersecurity.
- Anti-Phishing Working Group (APWG):
- Organizations like the Anti-Phishing Working Group (APWG) Provide Valuable Resources and Training Materials:
By utilizing these tools and resources, individuals and organizations can build a robust defense against phishing attacks. Combining advanced email security solutions, browser extensions for safe browsing, and comprehensive awareness programs ensures a multi-layered approach to cybersecurity, reducing the likelihood of falling victim to phishing schemes. Regularly updating and expanding your knowledge and defenses can keep you ahead of evolving threats and maintain a secure digital environment.
Conclusion
Phishing attacks are a significant threat, but with the right knowledge and tools, they can be effectively mitigated. By staying vigilant, educating yourself and your team, and implementing robust security measures, you can protect your personal and organizational data from these malicious attempts.


